TVRA, Security Audits & Benchmarking
What’s the basis for every effective security and risk management plan? Accurately identifying risks and vulnerabilities. And giving you the critical intelligence you need to protect what’s important to you.
Our team of proven experts – in counterterrorism, countertheft, electronic security, cybersecurity, physical security and more – identify and analyze the threats, vulnerabilities and risks facing your organization. The information we uncover sets the stage for potent protection plans for critical assets, infrastructure and personnel.
Aviation. Commercial. Critical infrastructure. Cultural and community. Sports. Education. Energy. Government. Healthcare. Hospitality and Gaming. Residential. Research. Transportation. We provide TVRAs, security audits and benchmarking for all these facility types and more.
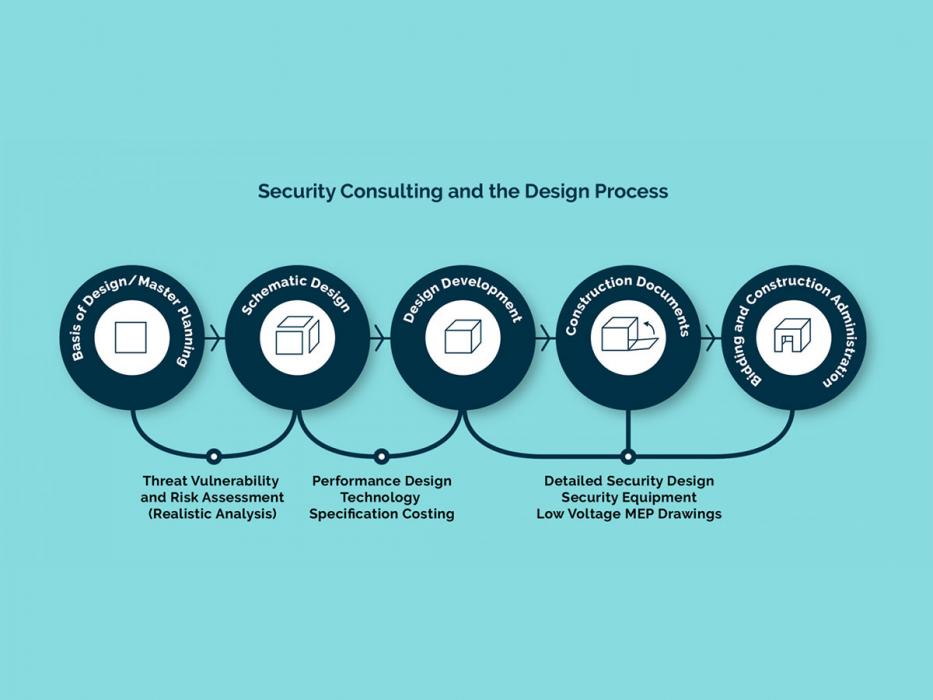
Threat, Vulnerability & Risk Assessment (TVRA). TVRAs establish your baseline threat profile and security posture. Detailed analysis. Customized, cutting-edge modeling. Virtual reality simulations. We use all these, and more, to assess the full range of physical vulnerabilities. And our cybersecurity TVRAs evaluate and test your systems against an array of threat-vulnerability scenarios.
We’re redefining the effectiveness of TVRAs by combining detailed on-site assessments with new analysis and visualization methods. Several cutting-edge tools – many developed in house – help us make the most accurate assessments and clearly communicate our findings.
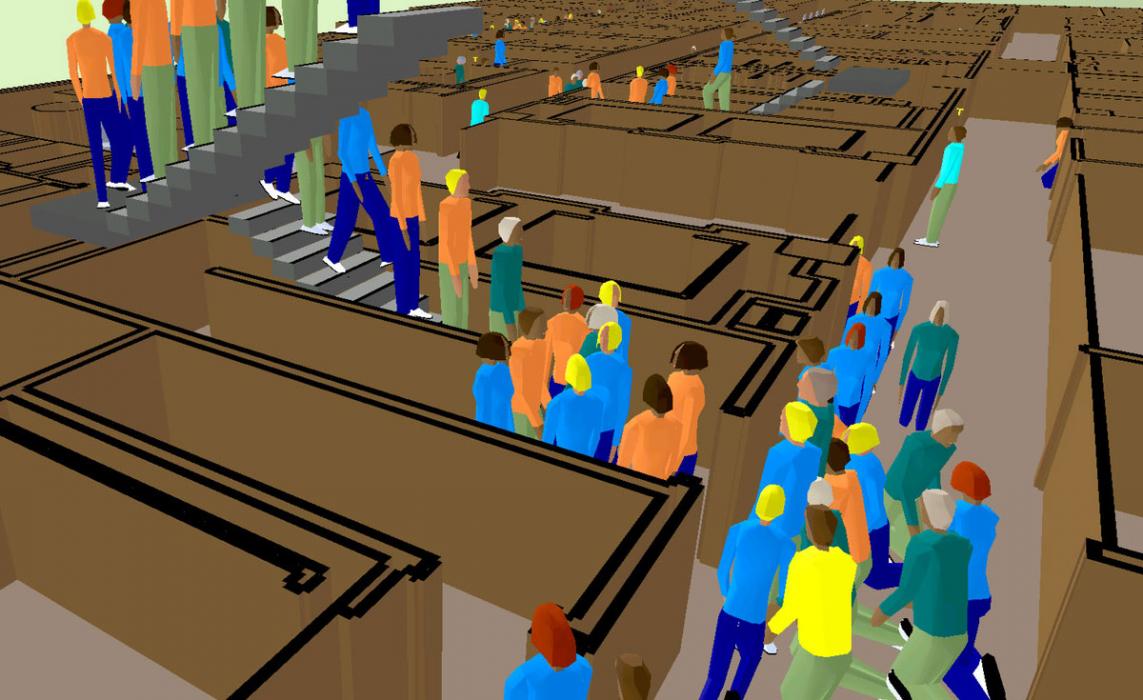
Escape and Evacuation Modeling (E&E). Our security experts can realistically predict human responses to specific emergency incidents. Simulations use a sophisticated human-behavior model to account for every building occupant as they interact with others, the structure itself and hazards such as fire, smoke, toxic products and more. These models have several uses. They test existing evacuation plans – validating them or showing where improvements are needed. They also allow structural engineers to design options that prioritize occupant safety.
Active Shooter Analysis. We’ve partnered with the developers of the buildingExodus E&E modeling package to extend its capabilities to active-shooter scenarios. For any given shooter location, we can calculate how long every occupant is exposed to the line of fire and quantify danger levels based on proximity to the shooter. The enhanced tool is a powerful new way to analyze – and mitigate – risk in crowded spaces, government buildings, campuses and more.
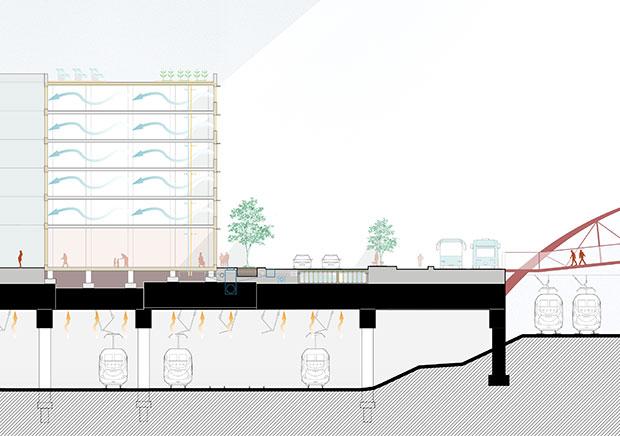
WALAIR: Airblast Environment Prediction | Fragmentation, Flight and Causality Estimation. This proprietary analysis program quantifies loads from explosions and applies them to accurate models of your facility. It helps our experts predict an explosion’s effect on the structure and on people – including eardrum and lung damage, tertiary injuries and risk of fatality. The software also provides fragment-flight impact velocities and casualty estimations.
Model results highlight vulnerabilities and inform our risk-mitigation recommendations. The software also enables direct comparisons between current conditions and performance with security upgrades, demonstrating the value of proposed security solutions.
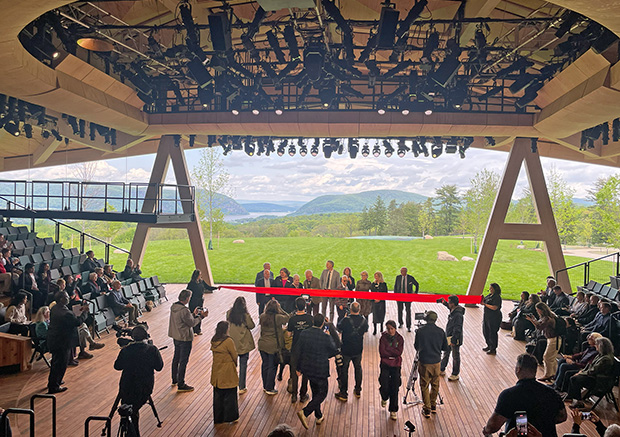
Virtual Reality (VR) Security Planning and Visualization. We’re breathing new life into our deliverable by bringing you into the project. We turn your floorplans into a 3D model, which we run through our proprietary VR software. Instead of reading a dry, hard-to-understand report, our realistic VR simulations let you see – and walk around in – before and after models. And then work directly with our team to quickly realize the design you envision. VR is a powerful decision-making tool that can help you save time and money.
Additional Services
U.S. DHS SAFETY Act Certification. Our security specialists are adept at applying our TVRA expertise to the regulatory demands of the SAFETY Act. We’ve provided guidance and technical support to owners of facilities ranging from stadiums and arenas to skyscrapers, bridges, tunnels and more. We provide a turnkey process – collaborating with proven law firms – that shepherds the process from TVRA, through application submission, to approval, implementation and commissioning, and renewals.
Security System Audits. How good is your security right now? We can perform a thorough review and objective evaluation of your equipment, design and procedures.
Security Benchmarking Studies. Our experts review your security measures to establish a baseline, then use empirical methods to benchmark your program against similar client types.
Related Capabilities
Expertise
Technology
Related News & Events
News
Risk Mitigation for Workplace DesignNews
Pittsburgh Int'l Airport Featured in Modern Steel Construction